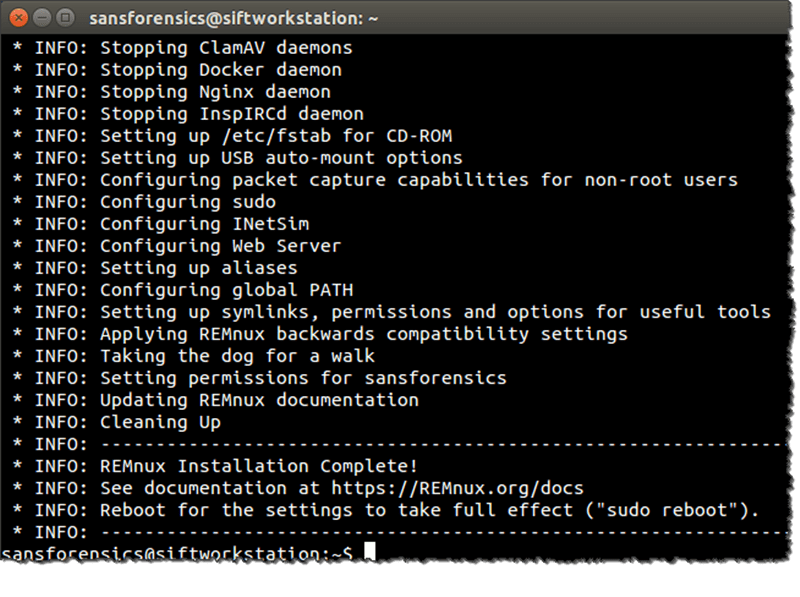
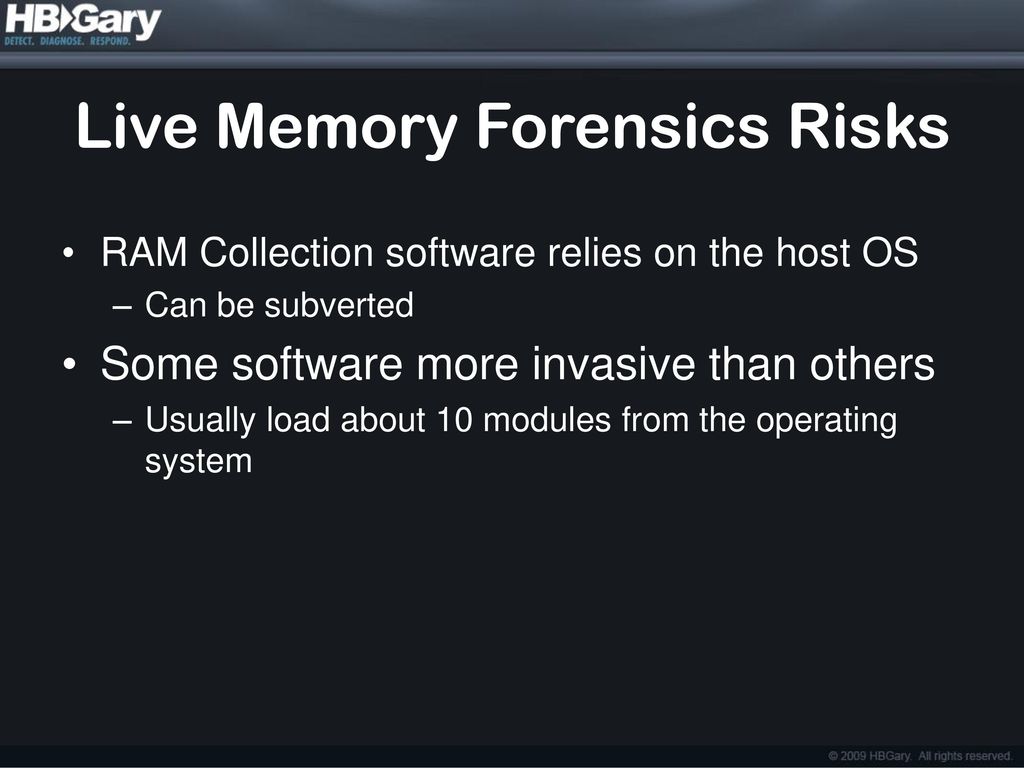
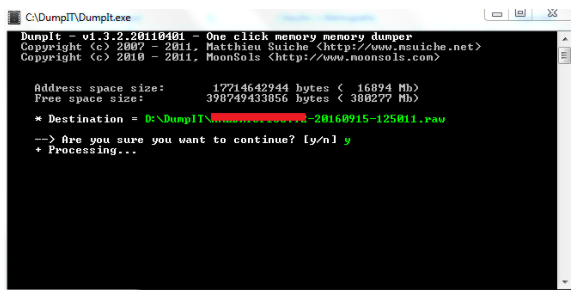
Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 14 (Live Memory Forensics) « Null Byte :: WonderHowTo

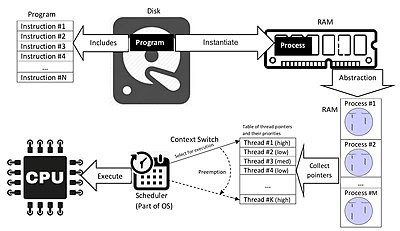
Signature based volatile memory forensics: a detection based approach for analyzing sophisticated cyber attacks | SpringerLink

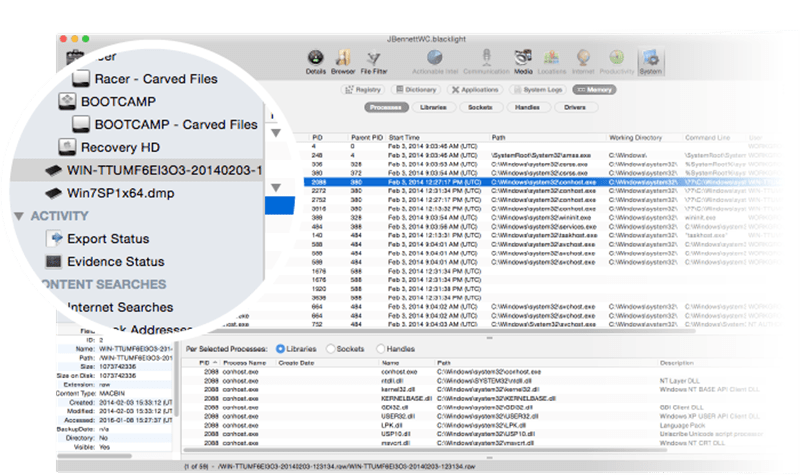
The Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and Mac Memory: Hale Ligh, Michael, Case, Andrew, Levy, Jamie, Walters, AAron: 8601421705806: Amazon.com: Books

Signature based volatile memory forensics: a detection based approach for analyzing sophisticated cyber attacks | SpringerLink