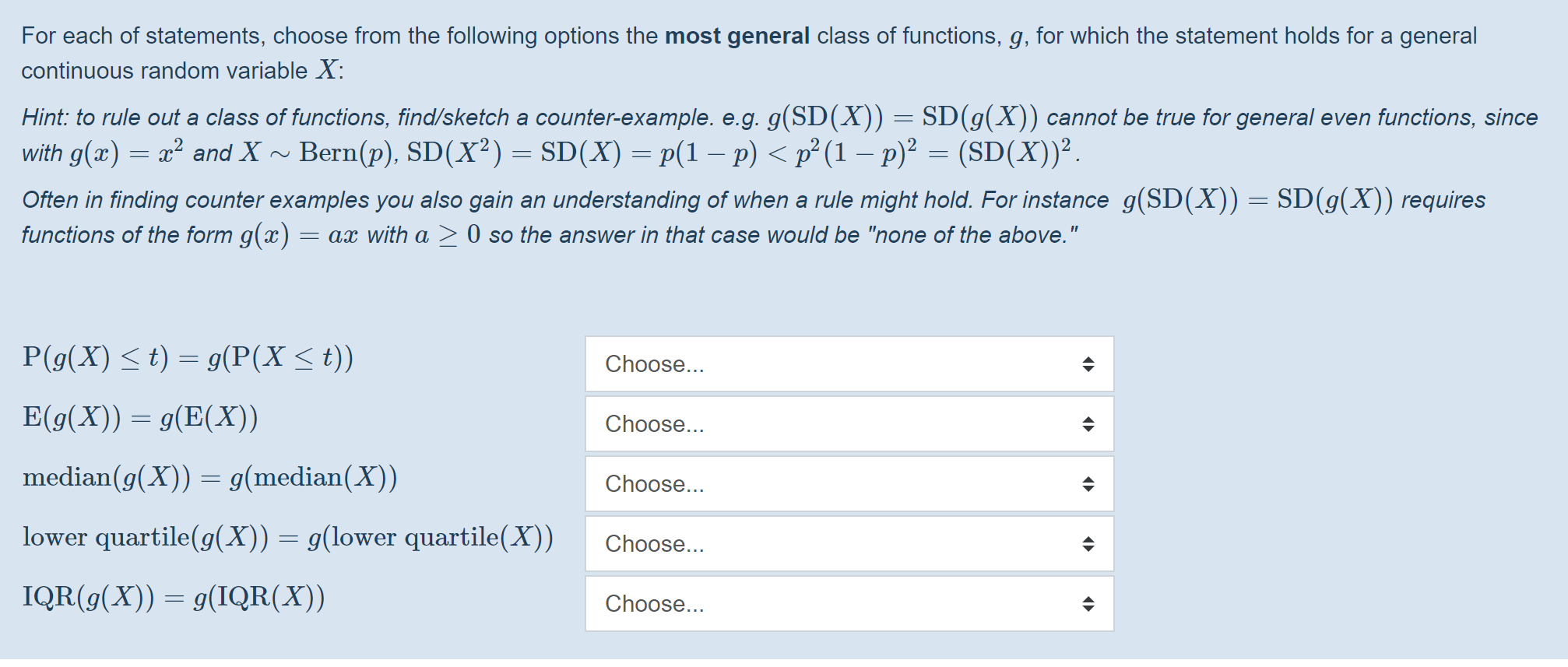
TPM based Virtual Monotonic Counters and Count-Limited Objects without a Trusted OS ∗ | Semantic Scholar
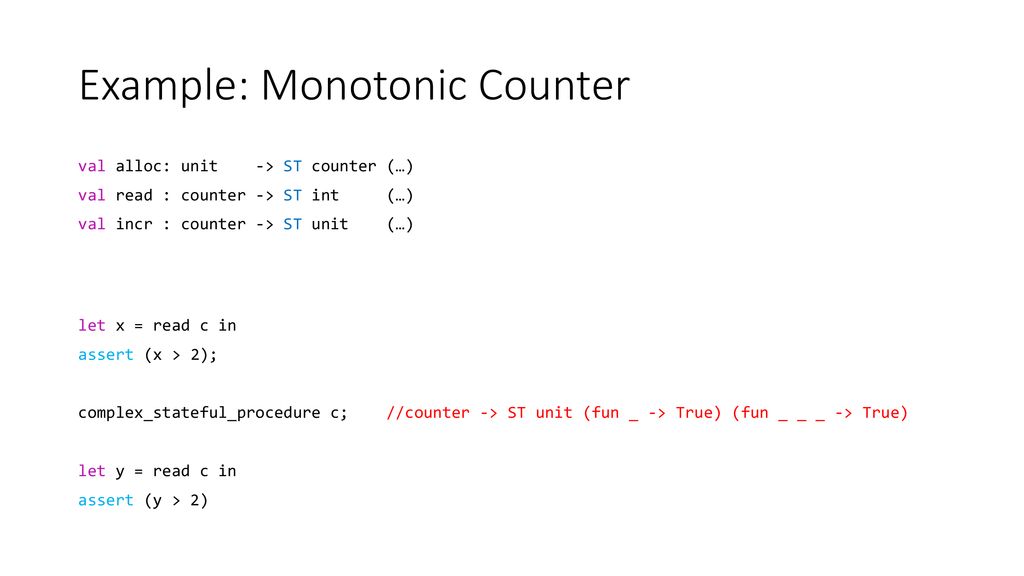
Virtual Monotonic Counters and Count-Limited Objects using a TPM without a Trusted OS (Extended Version)
PPT - Virtual Monotonic Counters and Count-Limited Objects Using a TPM without a Trusted OS PowerPoint Presentation - ID:943856

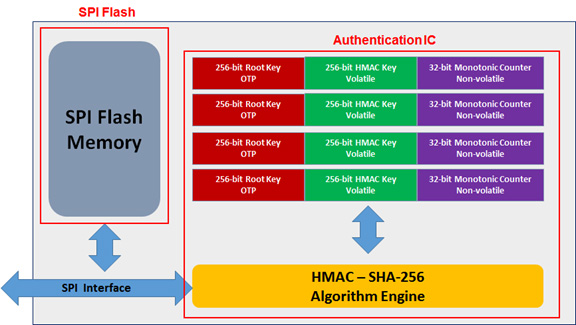
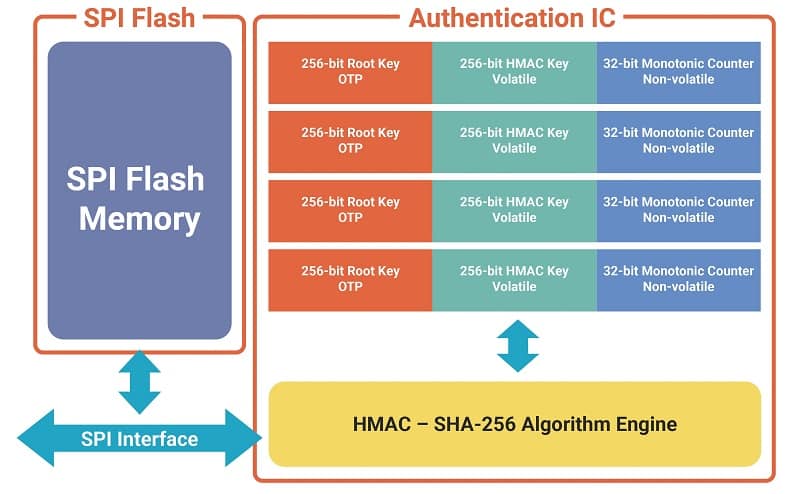
Micron Unveils Serial NOR Flash Interface With Replay-Protected Monotonic Counter For Ultrathin Devices IT Voice | Online IT Media | IT Magazine
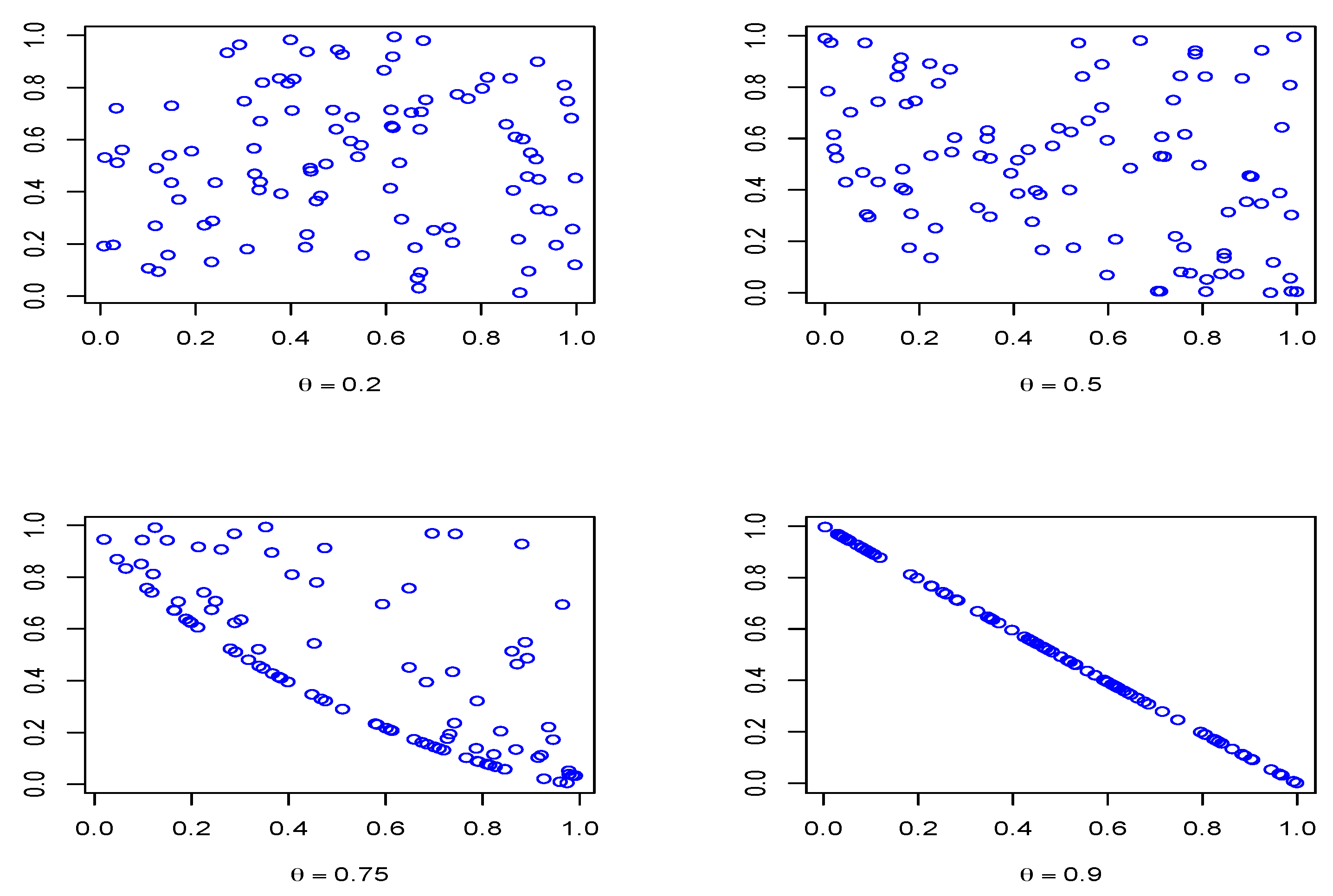
statsdreceiver] Counters are marked as monotonic · Issue #1789 · open-telemetry/opentelemetry-collector-contrib · GitHub
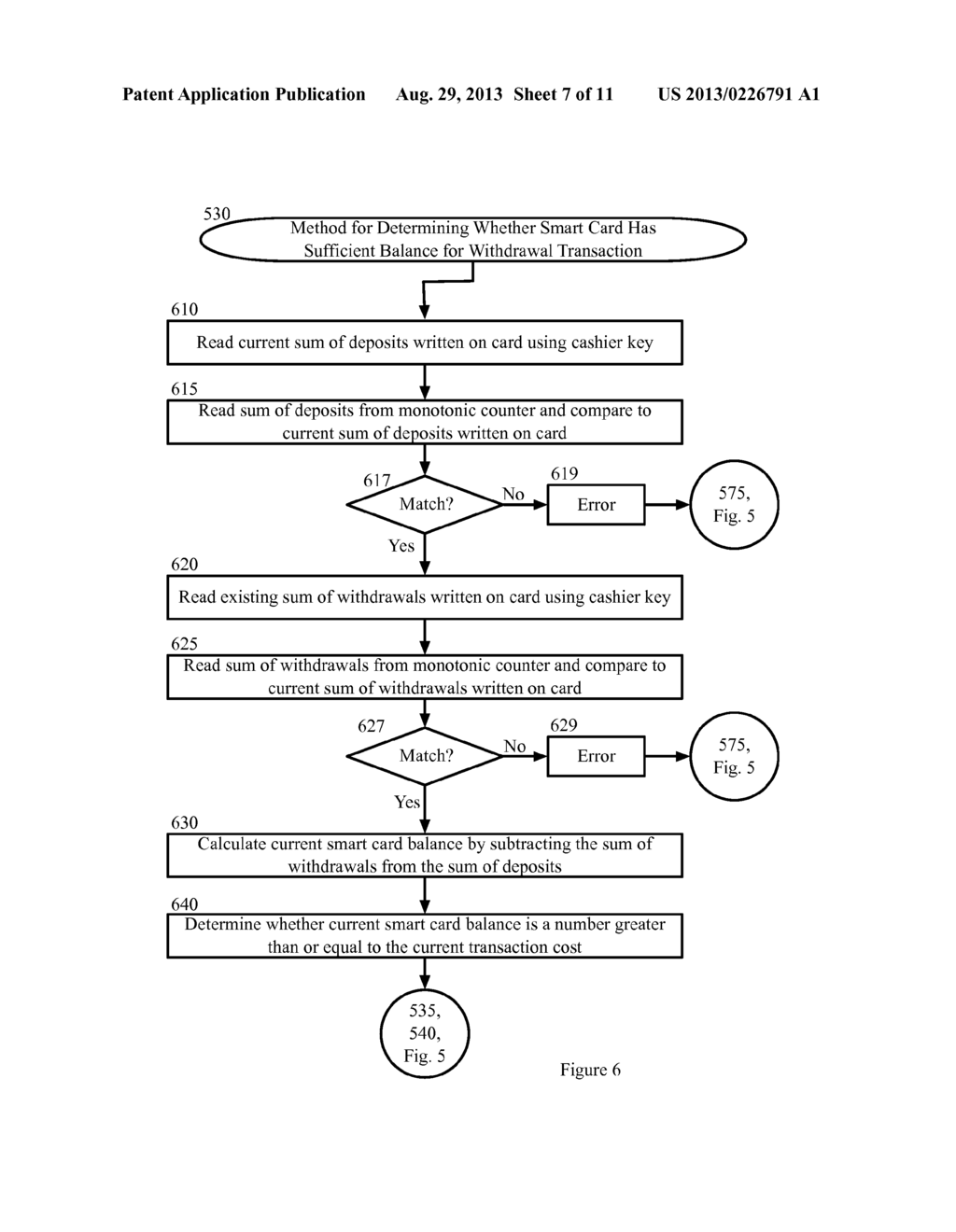
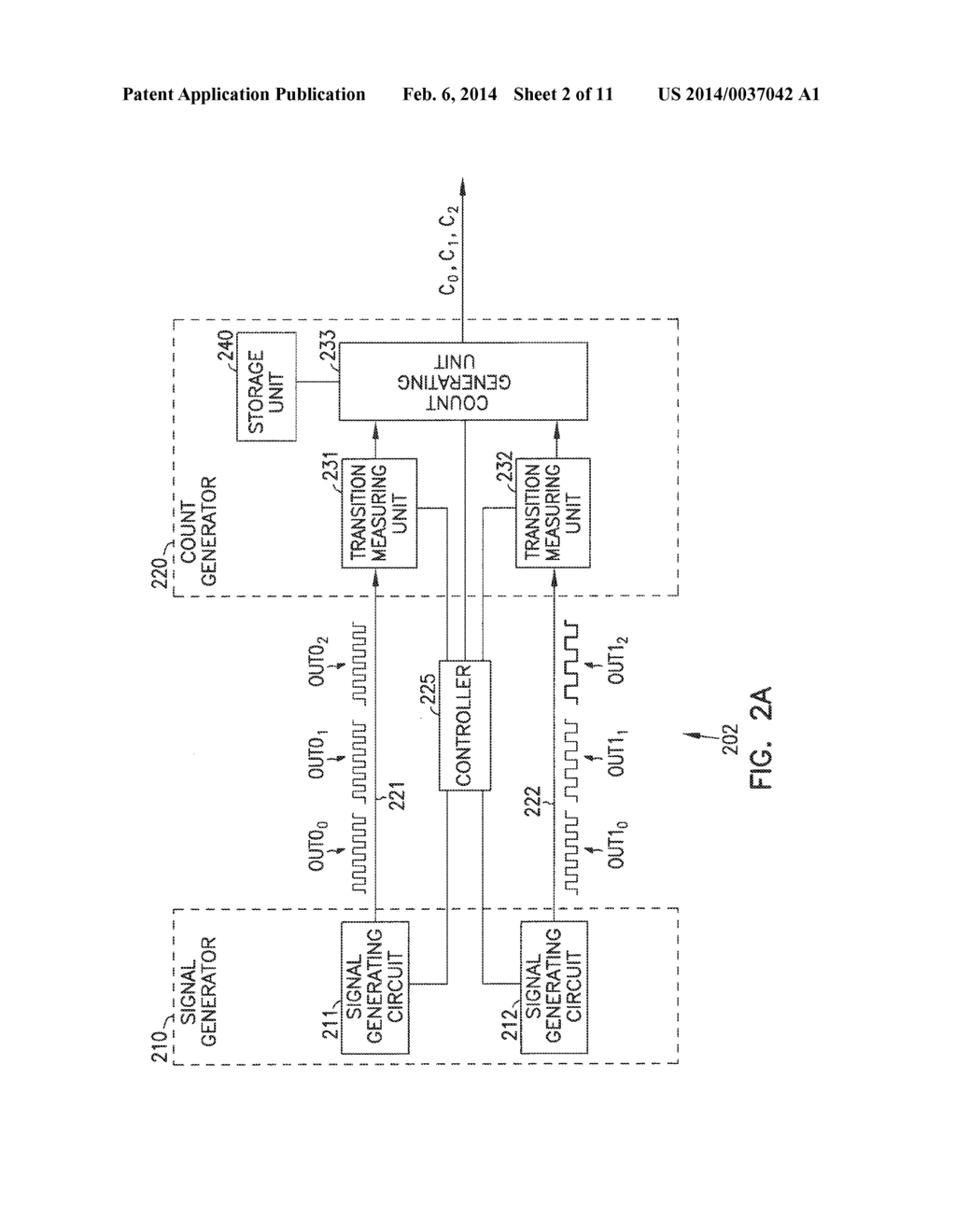
In-Card Access Control and Monotonic Counters for Offline Payment Processing System - diagram, schematic, and image 08

TPM based Virtual Monotonic Counters and Count-Limited Objects without a Trusted OS ∗ | Semantic Scholar
![PDF] Virtual monotonic counters and count-limited objects using a TPM without a trusted OS | Semantic Scholar PDF] Virtual monotonic counters and count-limited objects using a TPM without a trusted OS | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1fc71807dd748cde9798f1b305bc58c1252b0d38/5-Figure1-1.png)